Next.js 15 Middleware: A Complete Guide to RBAC and Multi-Tenant Security
Mastering Next.js 15 Middleware: The Backbone of Multi-Tenant Apps and Role-Based Security
Building a web application is easy, but building a scalable, secure, and professional multi-tenant system is a different beast entirely. If you are working with Next.js 15, Prisma, and Next Auth—much like the systems I develop during my breaks here in Saudi Arabia—you’ll quickly realize that security isn't just about a login page.
In a multi-tenant environment (where one app serves many different companies or users), you cannot afford to let "Tenant A" see "Tenant B’s" data. This is where Middleware becomes your best friend.
In this guide, we will dive deep into why Middleware is the secret sauce for RBAC (Role-Based Access Control) and how to implement it in a full-stack Next.js 15 environment.
Why Middleware is Non-Negotiable for Multi-Tenant Systems
When I first started building my Ads Management System, I faced a challenge: How do I ensure that a "Manager" can see the analytics, but a "Staff Member" can only upload images, all while keeping the "Super Admin" in total control?
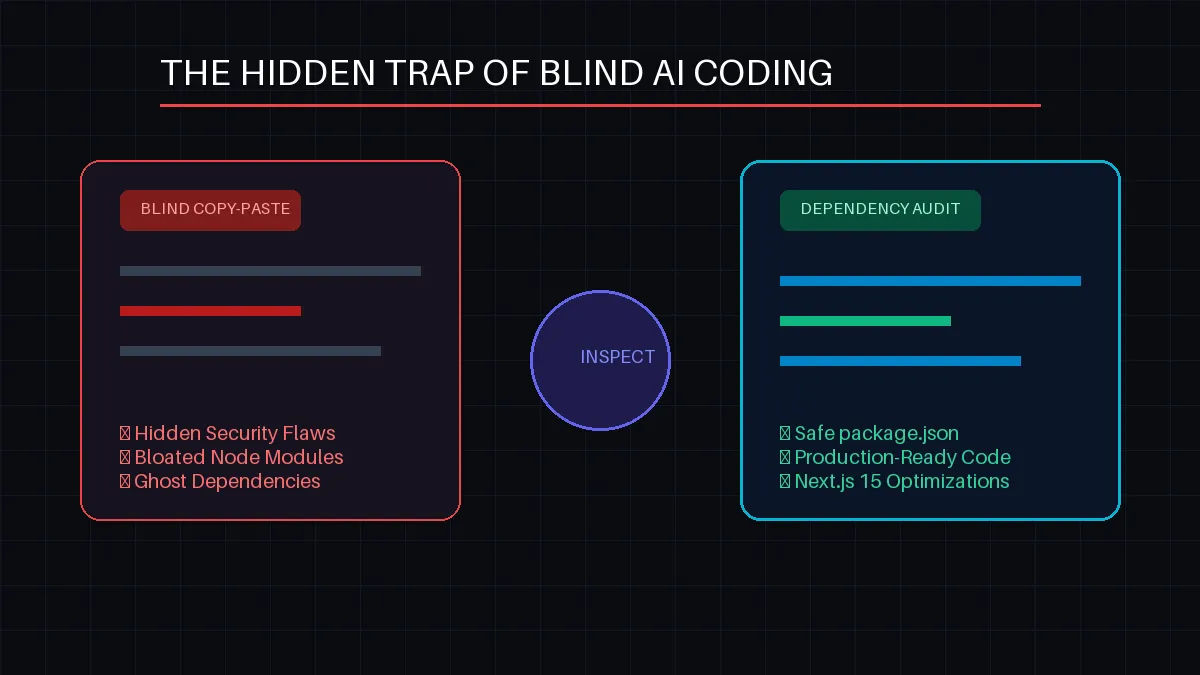
You might think, "I'll just check the user's role on every single page." Stop right there. That is a recipe for disaster. If you forget to add that check to just one page, you’ve created a massive security hole.
1. The "Gatekeeper" Philosophy
Middleware acts as a gatekeeper standing at the entrance of your application. Before a request even reaches your page or API route, Middleware inspects the user’s "ID card" (the Session Token). If they don't have the right role, they are turned away instantly.
2. Multi-Tenancy Complexity
In a multi-tenant app, you often have subdomains or specific path segments (e.g., app.com/tenant-1/dashboard). Middleware allows you to:
Extract the tenant ID from the URL.
Verify if the logged-in user actually belongs to that tenant.
Redirect them if they try to "URL-hack" their way into another company's data.
3. Server-Side Performance
Because Middleware runs on the Edge runtime (close to the user), it is incredibly fast. It prevents the server from doing the heavy lifting of rendering a page if the user isn't even allowed to see it.
The Tech Stack: Next.js 15, Prisma, and Next Auth
Before we code, let’s look at our foundation. We are using:
Next.js 15: For the latest App Router features.
Next Auth (Auth.js): To handle JWT sessions and roles.
Prisma: To define our roles in the database.